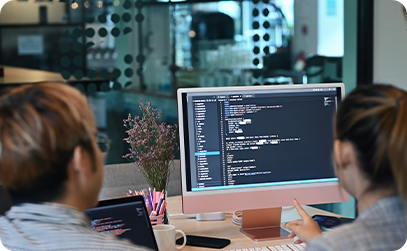
We Provide Cyber Solutions For Your Security
Conduct security assessments to identify vulnerabilities and assess overall security posture.


Conduct security assessments to identify vulnerabilities and assess overall security posture.

Evaluate the security practices of vendors and third-party partners.

Assist organizations in integrating security into their software development processes.
Read more
Conduct security awareness training for employees to promote a security conscious.
Read more
Assist organizations in meeting regulatory requirements related to data protection and privacy.
Read more
Assess the security of mobile applications for iOS and Android platforms.

Tools using to scan static source code and provide reports on security issues.
Read more


Risk Assessment-offering the process of identifying, analysing and evaluating risk, to ensure that the cyber security controls that are chooses are appropriate to the risks that an organisation faces.




Implementation of Secure SDLC- it gives the organisation to enable shift left focus on the application security standards early in the development process.
Engagements
Monitored Globally
Network Sensors


Qugiat nulla pariatur excepteur sint occaecat cupidatat no proident, sunt in culpa rui officia deserunt.

Ruis autem vel eum rui inea elit niau.

Guis autem vel eum rui inea elit niau.

Muis autem vel eum rui inea elit niau.

Euis autem vel eum rui inea elit niau.



Fugiat nulla pariatur excepteur sint occaecat cupidatat non proident, sunt in culpa rui officia deserunt mollit anim id est laborum incidunt ut labore et dolore magnam.
Molestiae non recusandae itaque earum rerum hic tenetur a sapiente delectus, ut aut reiciendis.